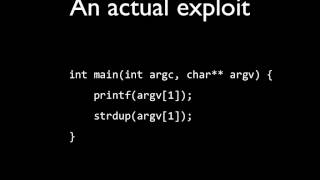
Web Reference: If the application uses Format Functions in the source-code, which is able to interpret formatting characters, the attacker could explore the vulnerability by inserting formatting characters in a form of the website. Apr 22, 2018 · I always had hard times to fully understand how to exploit Format Strings vulnerabilities. After a recent online challenge, I decided to tackle this problem and learn how to properly exploit them. Oct 21, 2024 · This article discusses the principle and possibilities of exploiting format string vulnerabilities, particularly in the C and C++ languages. The possibilities of exploiting the vulnerability are described in depth, and the auxiliary techniques used by the attackers are presented.
YouTube Excerpt: Hello hackers today we're going to be talking about
Information Profile Overview
Format String Exploits Introduction - Latest Information & Updates 2026 Information & Biography

Details: $4M - $32M
Salary & Income Sources

Career Highlights & Achievements
Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 3, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.



![Hack The Box - Introduction to Binary Exploitation - Leet Test - Format Strings [Walkthrough] Profile](https://i.ytimg.com/vi/b7urNgLPJiQ/mqdefault.jpg)


![Celebrity Intro Format String Vulnerability | PicoCTF 2017 [39] "I've Got a Secret" Profile](https://i.ytimg.com/vi/rkoP2mtwFNI/mqdefault.jpg)

