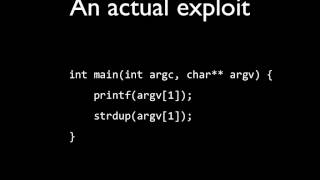
Web Reference: If the application uses Format Functions in the source-code, which is able to interpret formatting characters, the attacker could explore the vulnerability by inserting formatting characters in a form of the website. Oct 21, 2024 · This article discusses the principle and possibilities of exploiting format string vulnerabilities, particularly in the C and C++ languages. The possibilities of exploiting the vulnerability are described in depth, and the auxiliary techniques used by the attackers are presented. A format string vulnerability is a bug where user input is passed as the format argument to printf, scanf, or another function in that family. The format argument has many different specifiers which could allow an attacker to leak data if they control the format argument to printf.
YouTube Excerpt: Solving format1 from exploit-exercises.com with a simple
Information Profile Overview
Format String Exploit On An - Latest Information & Updates 2026 Information & Biography

Details: $77M - $88M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 4, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.