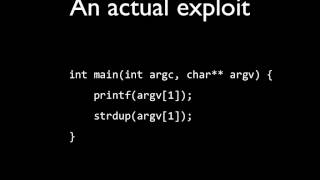
Web Reference: The printf exploit. In many programs compiled with older C compilers, it is possible to use a printf of a user-provided string to overwrite a value at any location in memory. Apr 22, 2018 · I always had hard times to fully understand how to exploit Format Strings vulnerabilities. After a recent online challenge, I decided to tackle this problem and learn how to properly exploit them. Cy Yombinator has cleverly protected the warehouses with Lockitall electronic lock devices. Lockitall locks are unlockable with an app. We've positioned operatives near each warehouse; each is waiting for you to successfully unlock the warehouse by tricking out the locks.
YouTube Excerpt: You can follow me on instagram : https://www.instagram.com/dali_wachani/ Check out the
Information Profile Overview
Microcorruption Ctf Format String Exploit - Latest Information & Updates 2026 Information & Biography

Details: $85M - $94M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 4, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.