Web Reference: Apr 29, 2022 · To calculate cryptographic hashing value in Java, MessageDigest Class is used, under the package java.security. This Algorithms are initialized in static method called getInstance (). After selecting the algorithm it calculate the digest value and return the results in byte array. The SHA (Secure Hash Algorithm) is one of the popular cryptographic hash functions. A cryptographic hash can be used to make a signature for a text or a data file. In this tutorial, let’s have a look at how we can perform SHA-256 and SHA3-256 hashing operations using various Java libraries. The SHA-256algorithm generates an almost unique, fixed-siz... The Java platform strongly emphasizes security, including language safety, cryptography, public key infrastructure, authentication, secure communication, and access control.
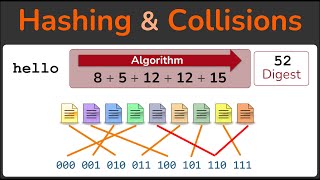
YouTube Excerpt: Hi guys we will learn in this tutorial series about the basics of
Information Profile Overview
Cryptography In Java 2 Hashing - Latest Information & Updates 2026 Information & Biography

Details: $78M - $110M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 4, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.