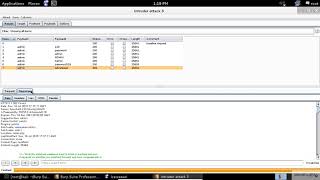
Web Reference: In this article, we will explore how to use Hydra to perform an HTTP form-based brute-force attack. We will discuss the necessary prerequisites, the step-by-step process, and some best practices to ensure effective and legal usage. See full list on golinuxcloud.com Feb 22, 2020 · In my opinion, using the Intruder feature within BurpSuite is an easier way to run brute-force attacks, but the effectiveness of the tool is greatly reduced when using the free community version. Instead of dealing with slow brute-force attempts, I decided to give Hydra a try.
YouTube Excerpt: You NEED to know these TOP 10 CYBER SECURITY INTERVIEW QUESTIONS https://elevatecybersecurity.net/interview ...
Information Profile Overview
Brute Forcing Web Forms With - Latest Information & Updates 2026 Information & Biography

Details: $70M - $94M
Salary & Income Sources

Career Highlights & Achievements
Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 4, 2026
Information Outlook & Future Earnings

Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.








