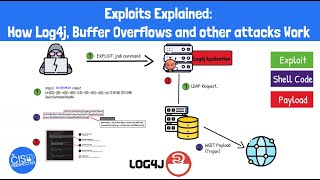
Web Reference: Oct 6, 2025 · Whether you're investigating a sophisticated malware campaign, solving a binary exploitation challenge, or conducting vulnerability research, the ability to quickly dissect and understand shellcode is invaluable. Jun 24, 2022 · Shellcodes can be divided into two categories; local or remote. The way they are categorised into these two groups depends on whether the attacker has gained control over the targeted device the shellcode runs on (local) or through a network (remote). Shellcode in the Exploitation Flow: This diagram shows how shellcode integrates into exploitation. After gaining control via a vulnerability, the attacker injects shellcode bytes and redirects execution.
YouTube Excerpt: 50 Shades of
Information Profile Overview
Vulnerability Exploitation With Shellcode Encoding - Latest Information & Updates 2026 Information & Biography

Details: $36M - $76M
Salary & Income Sources

Career Highlights & Achievements

Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: April 6, 2026
Information Outlook & Future Earnings
Disclaimer: Disclaimer: Information provided here is based on publicly available data, media reports, and online sources. Actual details may vary.








